[UPDATE] An update from the same user, just 7 hours after the original post, has now confirmed that the issue has been resolved, with the user also posting full details of the exploit. Viewing profile links and the activity feed is now safe again for Steam users.
The vulnerability was found in Steam's 'My Guides showcase'. The multi-guide showcase parsed scripts in the guide titles, allowing users to inject code by placing guides with scripts in the titles in their showcase.
This enabled malicious users to target others that simply clicked on their profile link with the methods described in the original article, which follows below.
[ORIGINAL ARTICLE] A post on the /r/steam subreddit by moderator R3TR1X today warns users of a potential threat when viewing user profiles as well as their own activity feed.
The post advises Steam users against viewing suspicious profiles and recommends disabling JavaScript in their browsers. The post further states that proofs of concept have been forwarded to Valve security, which is working to fix the issue.
A further post from user DirtDiglett, who created the proof of concepts, explains what the exploit can do, with the user only having to click on another user's profile.
Redirect you to any non-steam page, for example a phishing login page. From a user perspective it is you going to a legitimate Steam profile, then you see a login page. Seems legit right? Pop in your info. You didn't click anything suss so it's no big deal.Utilize scripting to use your Steam Market funds on any item the malicious user chooses, you wouldn't even need to confirm anything as you're on a valid login session.
Manipulate elements on the page as they see fit.
This essentially means that the malicious user would have full access to your active log on session and could perform any action as you. The information provided is deliberately vague about the nature of the exploit other than to mention the involvement of JavaScript.
Some may question why the users chose to make the exploit public at all, rather than just contacting Valve privately, but DirtDiglett answers that very question later in the thread.
It was already being abused before we started this thread. Valve Security has been made aware of the exploit, how it functions, and ways in which it can be exploited. It is trivial to fix, and once they see it it will be fixed in moments. We as a Steam community subreddit can't stop the spread of the information but we can at least try to make the community aware.
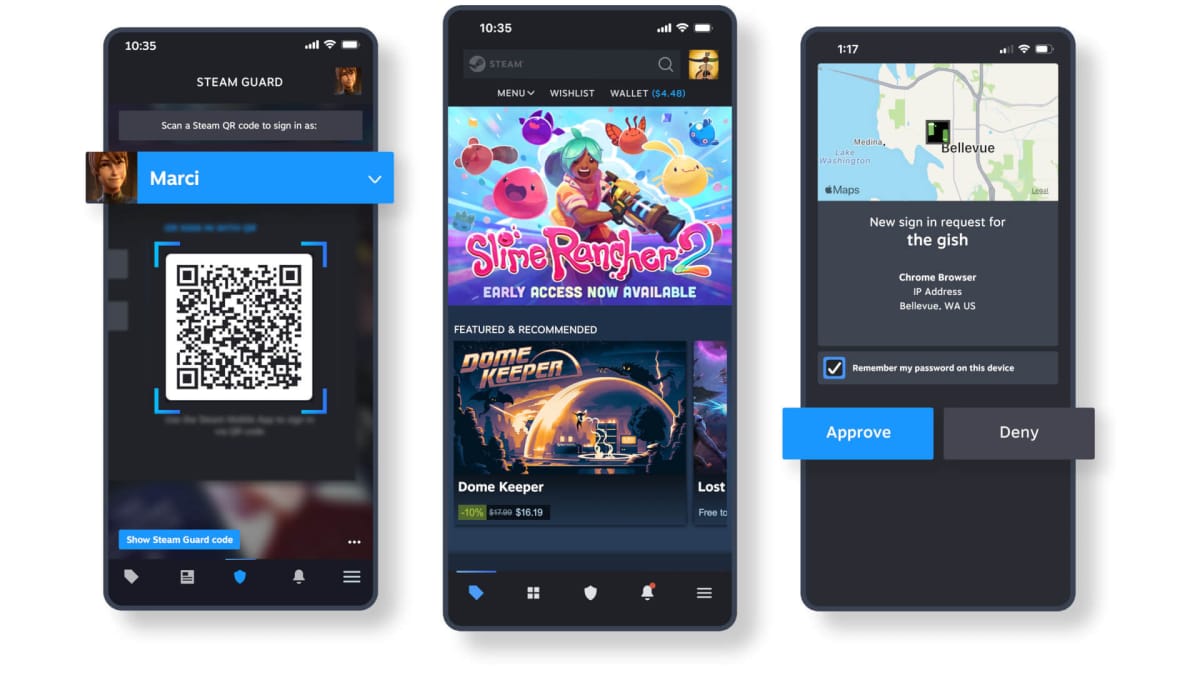
The exploit affects all browsers, including the Steam client itself. The best way to avoid the issue until it's resolved is by avoiding clicking on user profile links and enabling mobile or two-factor authentication on your account. For users who are possibly affected by the issue, the best advice is as found in the subreddit post.
Change your Steam Account password, enable Mobile Authenticator if it's not on already (otherwise deauthorize Steam Guard on all systems from settings) then restart your modem/change IP. You might want to also consider scanning your system with a malware scanner/anti-virus.
In response to this issue, the Counter-Strike: Global Offensive trading community subreddit, /r/GlobalOffensiveTrade, has been closed until further notice, citing an 'Active Steam Community exploit' and linking to the post in question.
The community revolves around CS:GO skin trading and has advised that it would rather not encourage users to post profile links or trading links (as would normally bestandard practice for its members) while the exploit is active.
We've reached out to Valve for further comment and will bring you more on this exploit and Valve's response as it becomes available.