A federal judge has denied a request from the government to compel all people in a building to give up their fingerprints to unlock Apple iOS devices. Judge M. David Weisman of the District Court For the Northern District of Illinois called the government’s request “boilerplate”, “dated”, and seeing “extraordinary authority”.
The details of the actual case are still under seal. The decision does not note if it was the FBI or another agency requesting the warrant. However, the judge’s order makes note that the case is targeting a person suspected of receiving and trafficking child pornography. He agreed that the government was able to meet it’s burden of demonstrating probable cause to search the suspect and their home. However, the warrant request lacks a specific identification of the suspect, only the identity of someone “who is likely residing there”. The warrant requests permission to “compel any individual who is present at the subject premises at the time of the search to provide his fingerprints and/or thumbprints “onto the Touch ID sensor of any Apple iPhone, iPad, or other Apple brand device in order to gain access to the contents of any such device.”” Based on the broad nature of the request, it was denied.
Under the Fourth Amendment of the US Constitution, people in the US are protected against unreasonable search and seizure. Under the Fifth Amendment of the US Constitution, an individual cannot be compelled to testify against themselves in court or to assist law enforcement in making a case against them. While the courts have held that being forced to divulge a password to encrypted files is a violation of the Fifth Amendment, they have not extended that to being compelled to provide biometric information such as a fingerprint or an iris scan, as those are biological characteristics and not information in one’s mind.
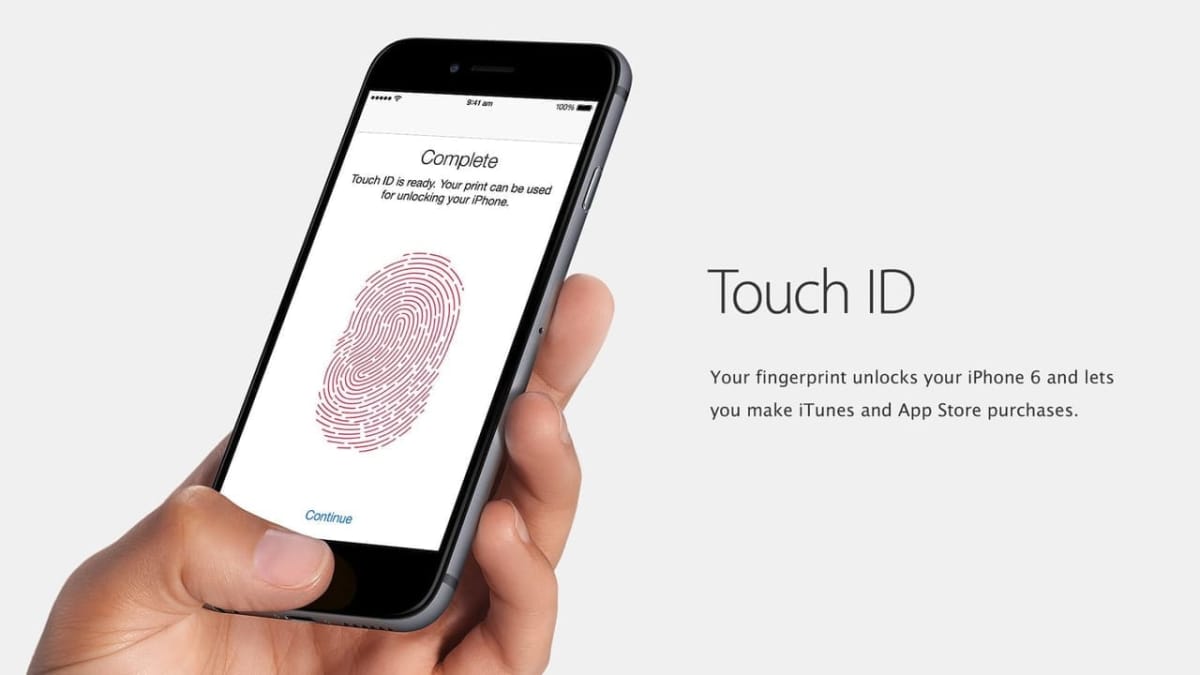
Apple’s TouchID system will allow a user to quickly unlock the phone, but only after it has been booted and idle for less than 48 hours. When a phone is turned on from a completely powered off state, it will require the passcode, as it will after a 48 hour idle period. If it requires the passcode, the suspect cannot be compelled to unlock the phone as it would divulge the contents of their mind. This is also not considered a search under the Fourth Amendment, being similar to being photographed or having a breathalyzer test performed.
The judge was also unusually critical of the structure and descriptions used in the application for the warrant. “the Court notes that some of the "boilerplate" background information included in the warrant is a bit dated, such as its explanation that "[t]he internet allows any computer to connect to another computer [so] [e]lectronic contact can be made to millions of computers around the world;" its explanation that a "Blackberry" is a common "Personal Digital Assistant” and its suggestion that the use of "cloud technology" is the exceptional way of transferring files and that transferring images to a computer by directly connecting a cable to a camera or other recording device is the expected means of data transfer”. He also notes that it disregards the possibility of security issues that can arise from wireless service.
As stated, the specifics of this case are still under seal, so it’s unclear what prompted the government to make such an unusual request, as well as how they gathered the information for the warrant application. This case has important Fourth Amendment and Fifth Amendment implications, so we will update this story as more details are released.