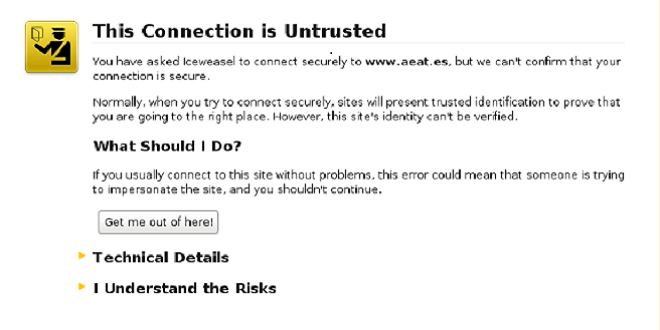
A major security flaw has recently been discovered, one that has left much of the internet vulnerable. The nature of this vulnerability is interesting; one could force a browser to use a weaker 'export-grade' encryption, then crack said encryption in just a few hours. These websites are then vulnerable to 'man-in-the-middle' attacks, an attack that leaves two parties convinced that they are in communication with each other, while in fact relaying their communications to a third party, acting as an intermediary. Notable site effected by this vulnerability include the websites of the White House, The FBI, and the NSA.
The last one come with a chuckle.
The origin of this vulnerability is certainly interesting. During the advent of Secure-Socket-Layer encryption (SSL), the NSA insisted that Netscape release a 512-bit encrypted version internationally, solely so that the NSA could better decipher and read foreign web traffic. It will be left to the imagination of the reader why the NSA would want such a thing. Despite a rule change in the year 2000 allowing any browser to use higher security SSL, by then the older code was unfortunately a fixture in much of the web. But what is perhaps more disturbing about this story is that it reveals that code that is well older than fifteen years is still being used on the internet. It would appear that certain pieces of internet infrastructure are crumbling.
This flaw has been labeled FREAK by researchers, short for Factoring attack on RSA-EXPORT Keys.
TL:DR; It is all the NSA's fault.
Reporting on this story, ZDnet wrote:
All of this has happened because as Matthew Green, a cryptographer and research professor at Johns Hopkins University, succinctly put it, the NSA made sure that the early "SSL protocol itself was deliberately designed to be broken."Expressing many of the same concerns, the Washington Post writes:And, now, it has been. It's just that it's now open to being broken by anyone with basic code-breaking smarts and easily available computer resources. The key problem is that OpenSSL and Safari both contain bugs that cause them to accept "RSA export-grade keys even when the client didn't ask for export-grade RSA."
The problem illuminates the danger of unintended security consequences at a time when top U.S. officials, frustrated by increasingly strong forms of encryption on smartphones, have called for technology companies to provide “doors” into systems to protect the ability of law enforcement and intelligence agencies to conduct surveillance.While there is still much need for concern, companies are diligently working to patch this security flaw. While Google's Chrome browser is immune to FREAK, the stock browser on Google's Android OS remains unfortunately vulnerable. Both mobile and desktop versions of Apple's Safari browser are vulnerable to FREAK. On the other hand, domain name system server company CloudFlare was quick to announce that they had secured their SSL sites from vulnerability back in January....
Christopher Soghoian, principal technologist for the ACLU, said “You cannot have a secure and an insecure mode at the same time… What we’ve seen is that those flaws will ultimately impact all users.”
Are government agencies competent enough to know the consequences of asking technology firms to leave in vulnerabilities? Do they have the right to make such demands?