Windows has always had a problem with backwards compatibility. It does too much of it. Windows is made to be easy on the user by default, with minimal security, with the settings necessary to run a piece of software from Windows 98 still on by default in Windows 10. One example of this epidemic is Data Execution Prevention (DEP). DEP was added to Windows XP Service Pack 2. It's been around a while. If you force DEP on, Windows 98 compatible or XP service pack 1 compatible applications, which were compiled without it in mind, will crash. These are fairly rare these days, so running with DEP on is likely safer than running with it off. The TLDR is that it should be on, and you can skip to the how-to below. What is it: Data Execution Prevention is a security feature on modern operating systems that disallows execution of binary code in memory space that isn't marked for memory execution. Each memory location is marked by a NX bit, which can be a 1 or 0. Because of this, enabling DEP has no performance penalty, as the penalty already exists with it being off. If it's forced on, you become flat-out immune to many different types of attacks. By default—that ugly word that causes so many problems—all 64 bit applications, and all Windows components, have DEP enabled, but with any 32 bit application, it's the Wild West where anybody can choose to enable it or not enable it at compile time. Beyond that, any 32 bit application that chooses to enable it can include non-Microsoft DLLs that don't have it enabled. It is a security vulnerability because that allows a piece of malicious code to run inside your application via included DLL. If exploited, evil code can run Return Oriented Programming (ROP) attacks, which can open other attack venues. DEP on its own isn't sufficient to stop all execution based memory exploits, but combined with Address Space Layer Randomization (ASLR), which was introduced in Windows Vista and much improved in Windows 8, it stops the large majority of them. Now how to force it on globally!
Enable Data Execution Prevention (DEP) Locally
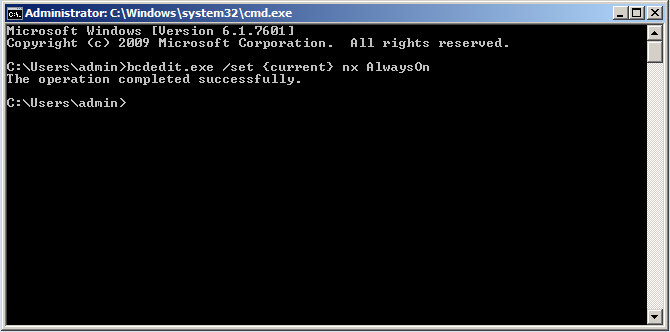
- Press start
- Type: cmd
- Rightclick cmd and run it as an administrator.
- Accept User Account Control permissons, using password as required.
- Type in your selected option
- Recommended: bcdedit.exe /set {current} nx AlwaysOn
- bcdedit.exe /set {current} nx AlwaysOff
- Default: bcdedit.exe /set {current} nx OptIn
- bcdedit.exe /set {current} nx OptOut
Enable Data Execution Prevention (DEP) via Group Policy Object
Active Directory Group Policy will allow a network administrator to distribute a rule to a large network to enable Data Execution Prevention without running to each machine. Group policy is not available for Windows home editions.
- On your Windows domain controller, open Group Policy Management
- Choose a Group Policy that only applies to machines that are Windows 7 or higher. (Windows Vista does not have Powershell unless you install it)
- Navigate to: Computer configuration > Policies > Windows settings > Scripts (startup / shutdown)
- Add a command startup script: "powershell set-execution policy unrestricted"
- Add this powershell script inside the Machine>scripts>startup folder of the GPO
- Set the script as following:
################################
##########################
Security is a complex thing, but there are many common exploit attack vectors that you can plug that apply to a large number of applications. Have questions? Have requests for other tech guides? Put them in the comments.
Have a tip, or want to point out something we missed? Leave a Comment or e-mail us at tips@techraptor.net