An imposter Pokemon GO app has made it’s way onto the Google Play Store in an attempt to swindle hopeful Pokemon trainers into compromising their security. Those that were waiting to download the popular AR application from The Pokemon Company and Niantic, or live in a region that the game hasn’t been officially released in yet should be wary of this fake version of the game when looking to download Pokemon GO.
Discovered by an IT security firm called Proofpoint the unofficial Pokemon GO app has a modified APK with a RAT. No rattata’s here, this APK contains a remote access tool which can give cybercriminals full access to the device it’s installed on. Having a RAT installed on your device means those responsible for the fake app will be able to modify and delete data, as well as track your location and take pictures and videos etc. Known as Droidjack or SandroRAT the malicious software was noticed less than 72 hours after Pokemon GO made it onto the store.
To avoid downloading a third-party infected Pokemon GO app do your best to ensure the authenticity of the application. The official app is from developer Niantic, Inc and is rated a “Top Developer” on the Google App Store. A link to the correct app is linked to from the official webpage.
The infected fake Pokemon GO is a risk for players that are side-loading APK’s from third parties; a tempting option for those who want to play the game before it has launched in their region. This can be done by going into security settings and enabling the installation of apps from unknown sources. If you don’t want to risk giving over control of your phone to cybercriminals then you shouldn’t risk side-loading Pokemon Go. Although the worldwide launch has been delayed to fix server problems, releases in many new regions is expected soon.
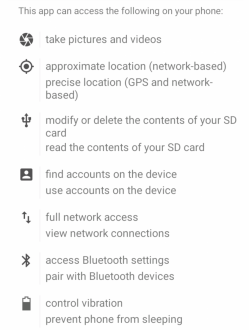
For those that aren’t sure if they’ve already been infected, they can check the SHA256 hash of their APK to see if it’s the malicious file already identified by Proofpoint here. The legitimate SHA256 hash is 8bf2b0865bef06906cd854492dece202482c04ce9c5e881e02d2b6235661ab67, although an official updated version with a different number may exist. Another measure is to look into the permissions of your Pokemon GO application and checking them against those of the legitimate version as shown in the picture below.
Malicious modified version of the Pokemon GO app look identical to the legitimate version so users should take a closer look if they side-loaded their Pokemon Go application. Not only will the malware compromise the security of the user's device it can compromise information on the networks it’s used on. For a more detailed look at the fake Pokemon GO application, Proofpoint's research into the matter can be read here.
This isn't the only malicious use that Pokemon GO has been put to, with armed robbers allegedly using it to help locate victims. In brighter news, Niantic confirmed that trading will be coming to Pokemon GO recently and if you want to find out more about the application taking over the world, read our review on it!







